What is AWS CodeCommit? Streamlining Source Control in the Cloud.
In the era of cloud computing, source control is a pivotal aspect of the workflow, ensuring that code changes are managed efficiently, collaborative efforts are streamlined, and the integrity of the codebase is maintained. Amazon Web Services (AWS) offers a robust solution for source control in the cloud with AWS CodeCommit. This article delves into the features, benefits, and use cases of AWS CodeCommit. We will also go ahead and create a code commit repository and clone the repo to our local machine, add files, commit and push them to our AWS code repository.
What is AWS CodeCommit?
AWS CodeCommit is a version control service hosted by Amazon Web Services that allows developers to store and manage their source code, binaries, and other assets in the AWS cloud. Additionally, it is designed to work seamlessly with existing Git tools, making it easy for developers to integrate it into their current workflows.
Key Features of AWS CodeCommit.
Fully Managed Service: AWS CodeCommit takes care of the backend infrastructure, so developers can focus on writing code. There are no servers to manage.
Scalability: CodeCommit can handle repositories of any size, with the ability to scale up as your project grows.
High Availability and Durability: your repositories are always accessible and your data is protected against loss.
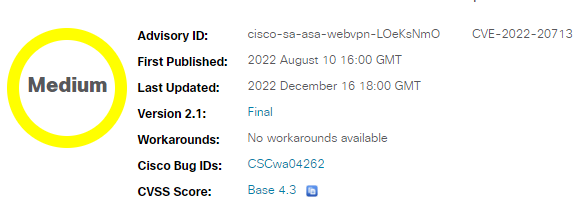
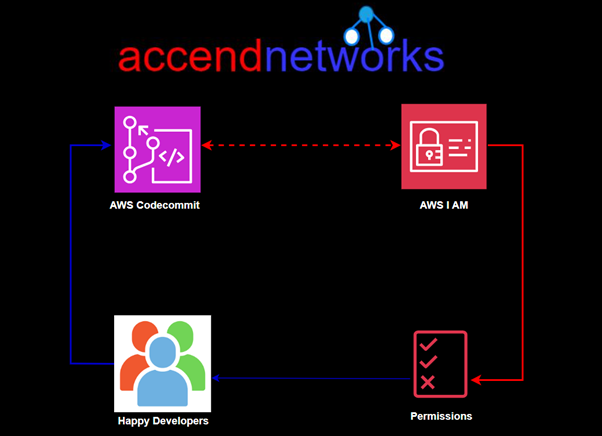
Security: CodeCommit integrates with AWS Identity and Access Management (IAM) to provide robust access control. You can use IAM policies to define who can access your repositories and what actions they can perform.
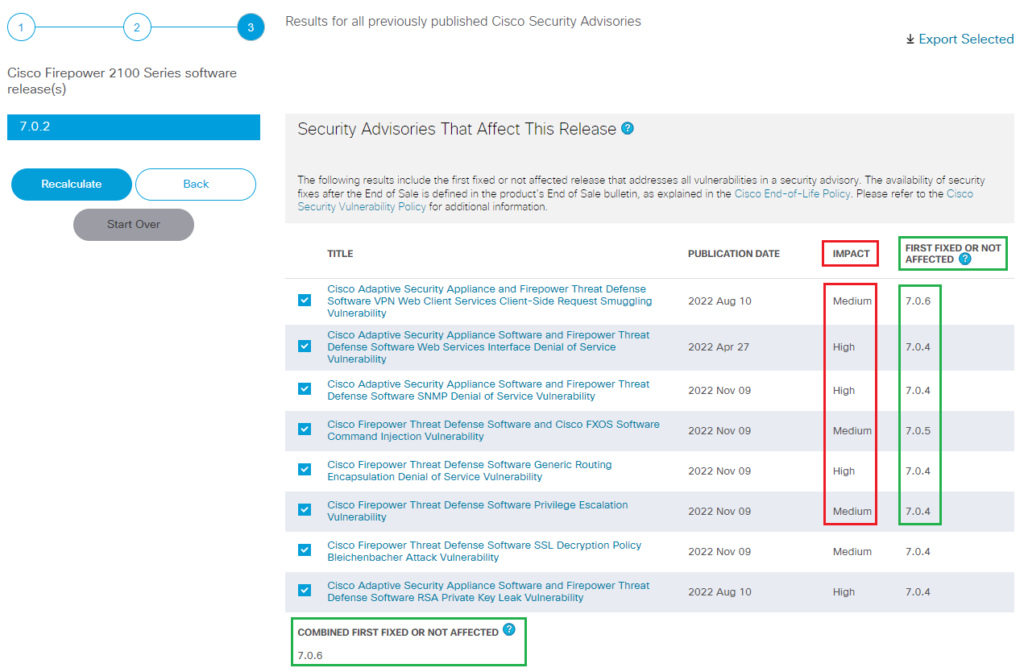
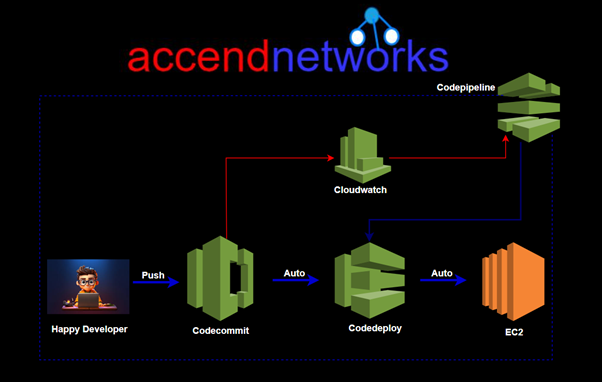
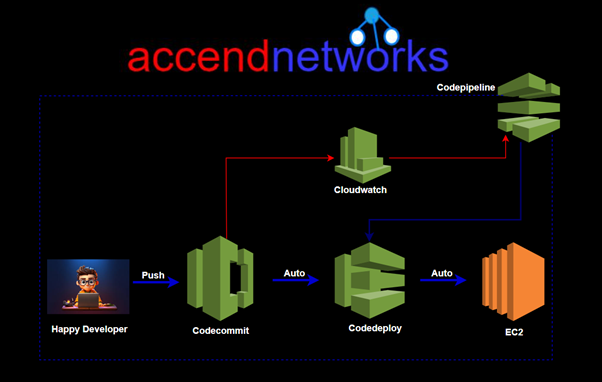
Integration with AWS Services: CodeCommit integrates seamlessly with other AWS services such as AWS CodeBuild, AWS CodeDeploy, and AWS CodePipeline. This allows you to create a complete CI/CD pipeline using AWS tools, enhancing your development and deployment workflows.
Standard Git Interface: CodeCommit supports the standard Git interface, so developers can use their preferred Git client, command-line tools.
Getting Started with AWS CodeCommit
Prerequisite.
Make sure you have full permission to Codecommit, or you can log in as an administrative user additionally, you should have git installed and configured on your machine.
Create a Repository
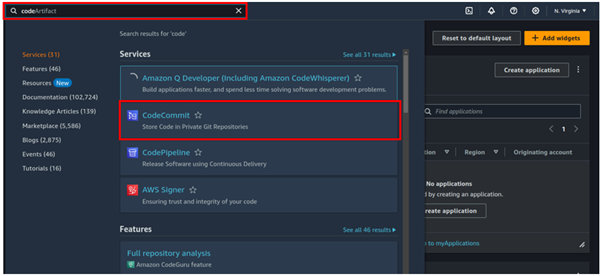
Log in to your AWS management console, in the search box, type Codecommit then select codecommit under services.
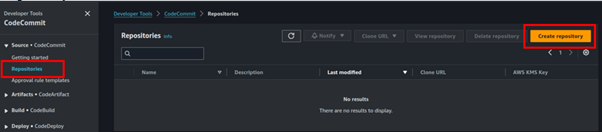
In the code commit UI on the left-hand side, select repositories then click Create Repository.
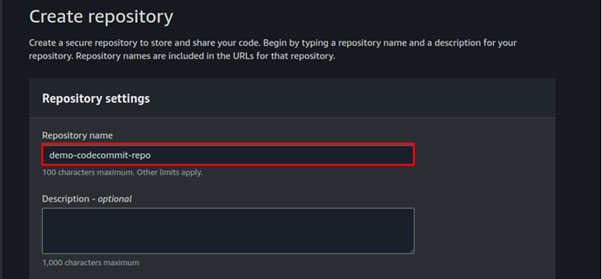
In the create repository dashboard, under repository settings, name your repo, will call mine demo-commit-repo.
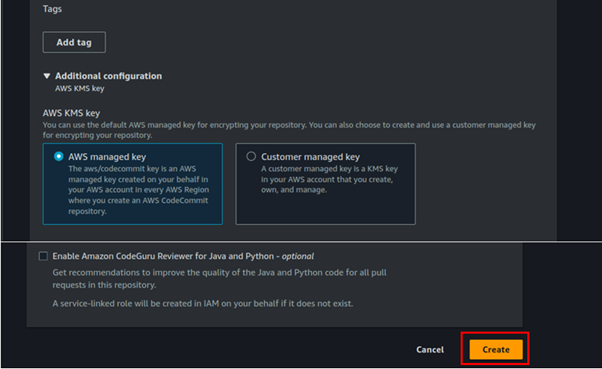
Codecommit is encrypted by default using KMS, but you can also choose your custom keys. We will leave it at AWS-managed keys with KMS.
Leave all other settings as default then click Create Repository.
Success, we are greeted with connection steps. We can see HTTPS, SSH, HTTPS(GRC).
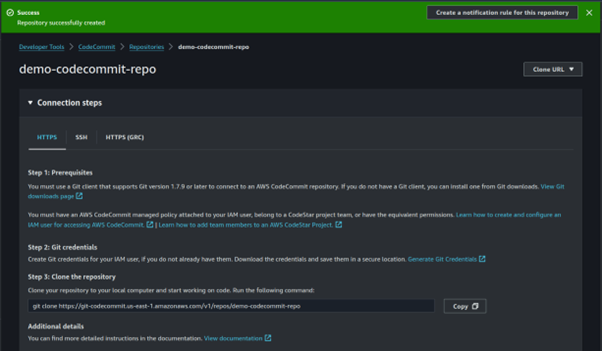
If you don’t see SSH then it means you are connected as the root user.
We will for now use HTTPS git credentials for Codemmit to connect to our git repository.
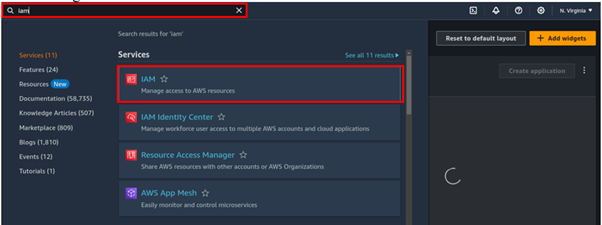
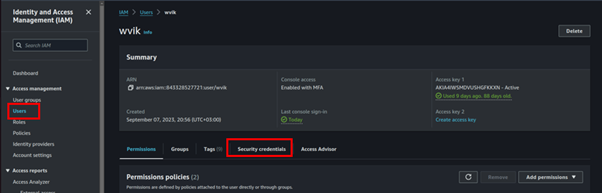
So let us log in to the I AM console.
Select users. Click your username, move to the security tab then scroll all the way down to HTTPS for git credentials.
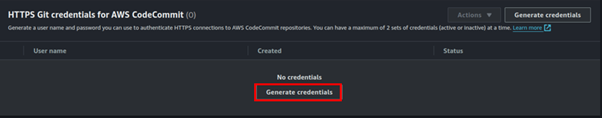
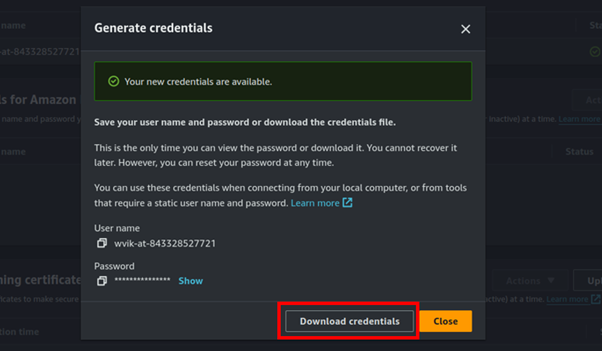
Click on generate and your codecommit credentials will be generated. Click the download button.
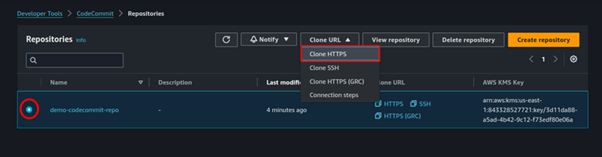
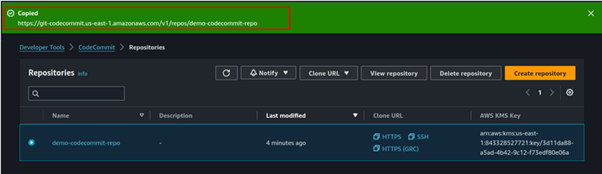
Go back to the codecommit repository select your repo then click the drop-down button of the clone URL then select clone HTTPS.
In this case, it will copy the HTTPS-type URL.
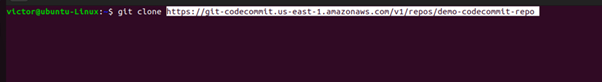
Use your preferred Git client to clone the repository to your local machine. This allows you to start adding code and making changes.
Go back to your terminal and type in git clone and paste in the cloned URL. When you press enter, you will be prompted for your username and password. Paste them in then press enter.
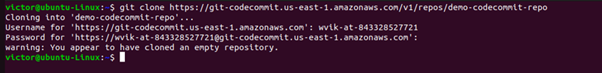
We have cloned our remote repo into our local machine.
With the repository cloned, you can push your changes to CodeCommit.
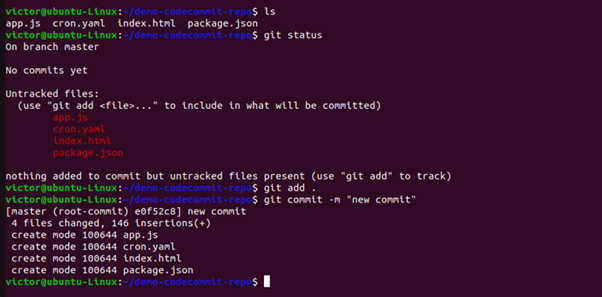
We will now copy a few files into our directory, commit these files, and push them to our remote repo.
Using linux command make sure you are in the repo directory then add copy files to your repo.

Using git add the files and then commit the changes as shown in the picture bellow.
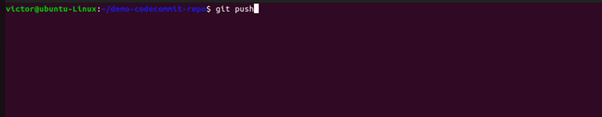
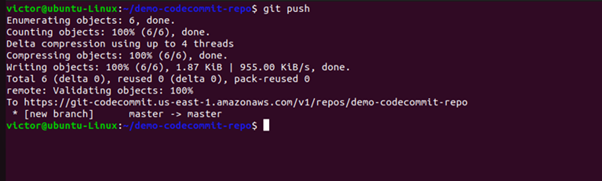
Once the changes are commited, you can then push them to the remote repo by using the below command.
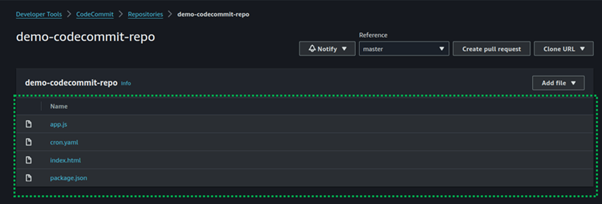
Now let’s go and check codecommit, and yes indeed the new files have been pushed to the codecommit repository.
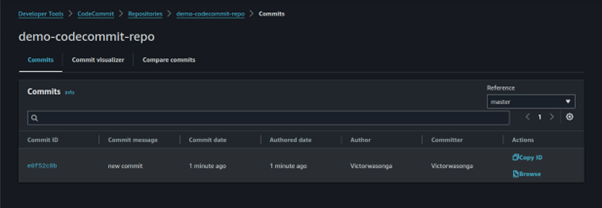
If you click on the commits on the left side of the repo UI, you can see the commit history.
This brings us to the end of this blog. AWS CodeCommit offers a powerful, secure, and scalable solution for source control in the cloud.
Thanks for reading, and stay tuned for more.
If you have any questions concerning this article or have an AWS project that requires our assistance, please reach out to us by leaving a comment below or email us at sales@accendnetworks.com.
Thank you!