AWS Hardware Security Module: Securing Your Keys in the Cloud

Introduction
As organizations increasingly move their operations to the cloud environment, the need for robust security measures becomes equally important. One critical aspect of this cloud security measure is the management and protection of cryptographic keys. This is where the AWS Hardware Security Module or AWS CloudHSM comes in handy. This article explores what CloudHSM is, its use case, and a demo of how to create one.
What is CloudHSM?
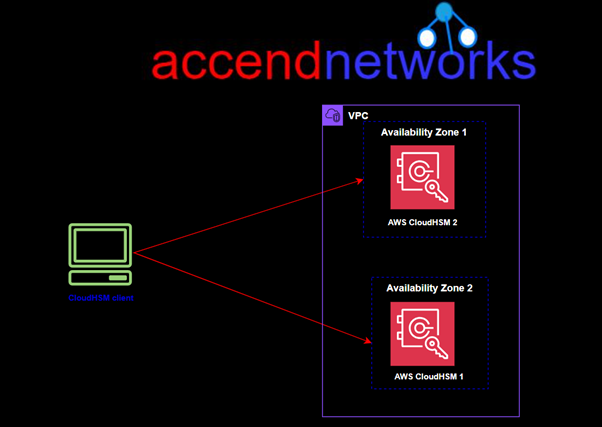
AWS CloudHSM is a cryptographic service for creating and maintaining AWS hardware security modules (HSMs) in your AWS environment. HSMs are computing devices that process cryptographic operations and provide secure storage for cryptographic keys. You can use AWS CloudHSM to offload SSL/TLS processing for web servers, protect private keys linked to an issuing certificate authority (CA), or enable Transparent Data Encryption (TDE) for Oracle databases.
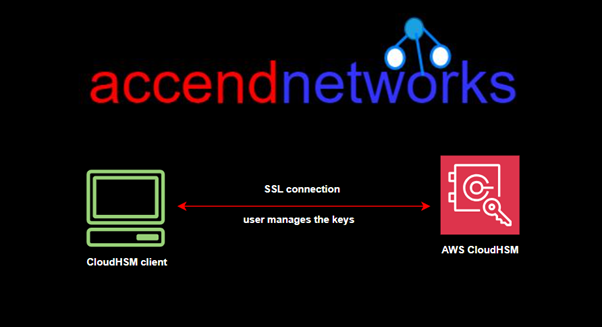
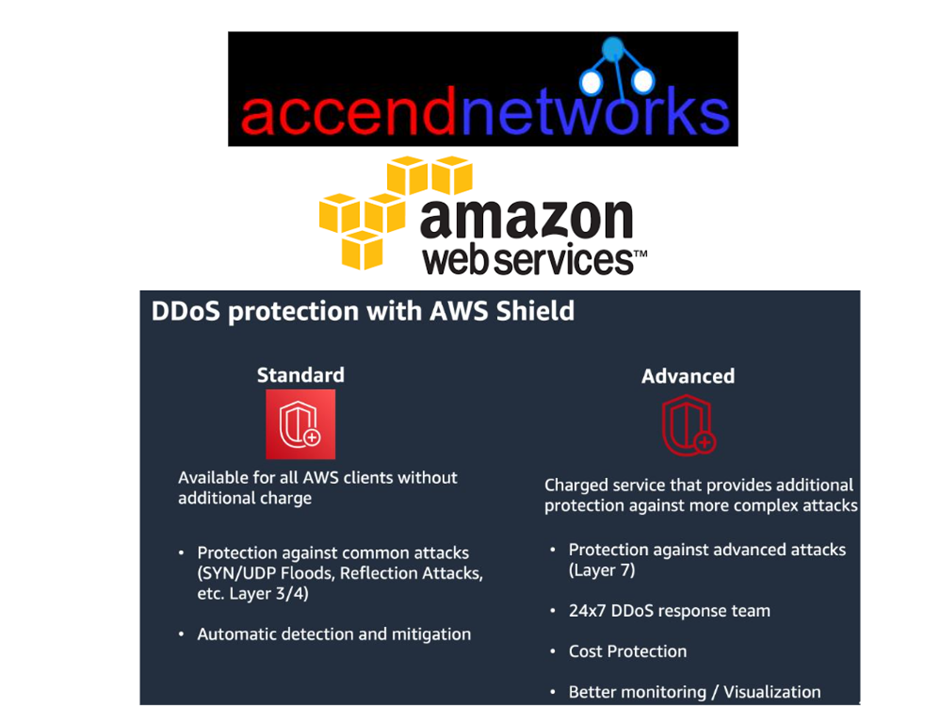
When we have the KMS, AWS manages the software for encryption and the encryption keys. But with cloud HSM, AWS only provides us with the encryption hardware. The HSM device is tamper resistant and has FIPS 140-2 Level 3 compliance. CloudHSM supports both symmetric and Asymmetric encryption.
Using AWS CloudHSM you must use CloudHSM client software since there is no API call for this service.
Key Features of Cloud HSM
Hardware-based Security: Keys are stored in hardware, which is inherently more secure than software-based storage.
High Availability and Scalability: Cloud HSM services are typically offered with high availability and can scale to meet the demands of enterprise workloads.
Compliance: Cloud Hardware Security Module is often compliant with industry standards such as FIPS 140-2 Level 3, ensuring they meet regulatory requirements for data protection.
Integration: Cloud HSMs can integrate with various cloud services and on-premises applications, enabling seamless cryptographic operations across different environments.
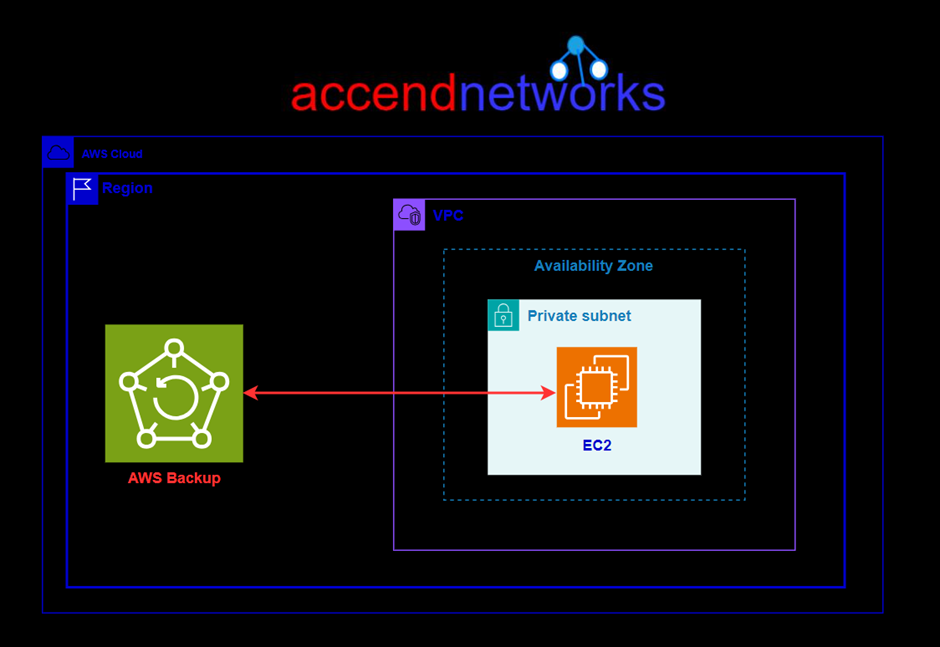
CloudHSM Backups
Backups are stored in Amazon Simple Storage Service (Amazon S3) within the same Region as the cluster. You can view backups available for your cluster from the CloudHSM console. Backups can only be restored to a genuine HSM running in the AWS Cloud. The restored HSM retains all the configurations and policies you put in place on the original HSM.
Creating a backup CloudHSM triggers backups in the following scenarios:
- CloudHSM automatically backs up your HSM clusters periodically.
- When adding an HSM to a cluster, CloudHSM takes a backup from an active HSM in that cluster and restores it to the newly provisioned HSM.
- When deleting an HSM from a cluster, CloudHSM takes a backup of the HSM before deleting it.
A backup is a unified encrypted object combining certificates, users, keys, and policies. It is created and encrypted as a single, tightly bound object. The individual components are not separable from each other. The key used to encrypt the backup is derived using a combination of persistent and ephemeral secret keys.
Backups are encrypted and decrypted within your HSM only, and can only be restored to a genuine HSM running within the AWS Cloud.
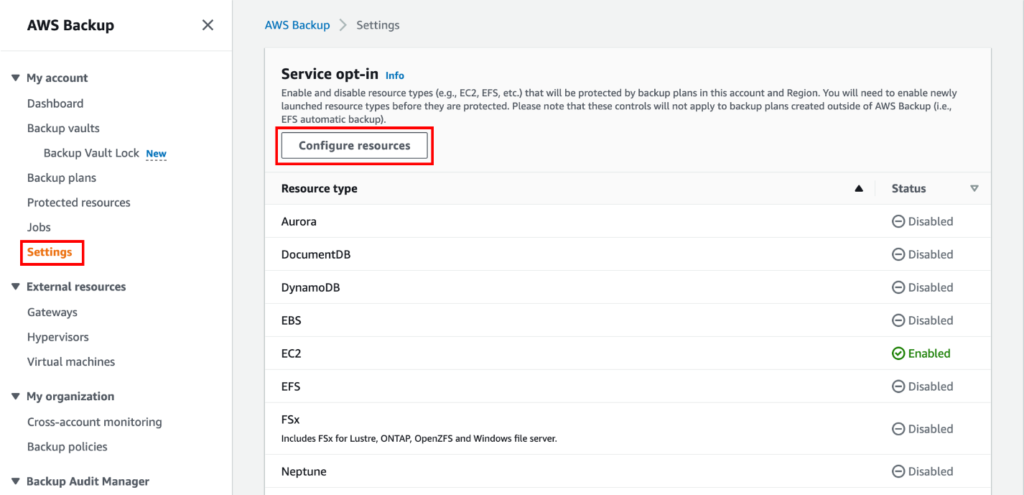
Let’s dive into the practical.
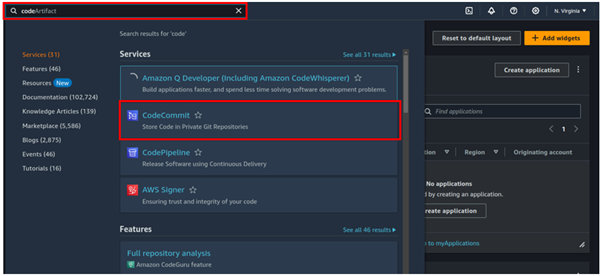
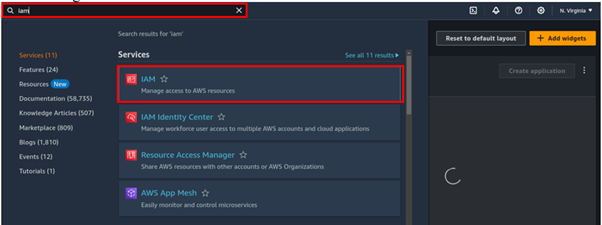
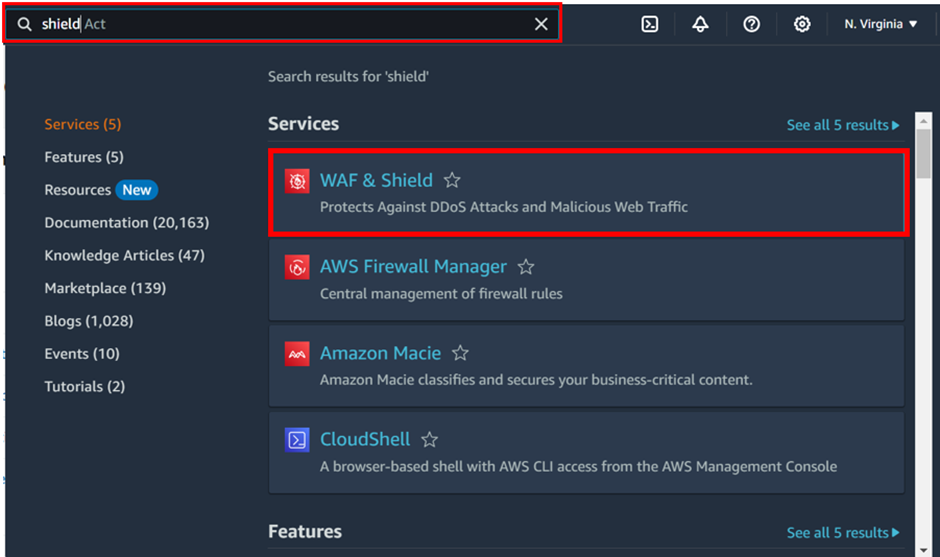
Login to the AWS Management Console then type CloudHSM in the search box then select it under services.
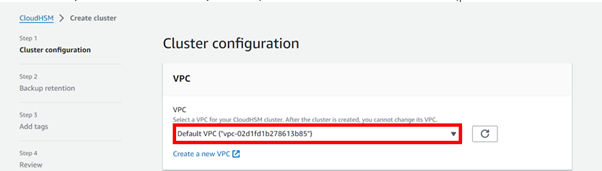
In the CloudHSM dashboard, click Create cluster.

In the create cluster dashboard, click the drop-down button and select your VPC, I will move with the default VPC.
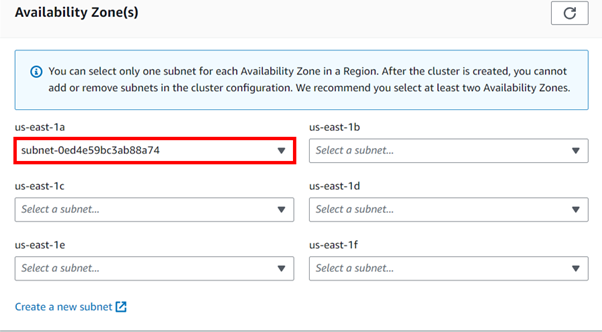
For subnet, you can only select one subnet per AZ, because I selected default VPC, I will move with the default subnet.
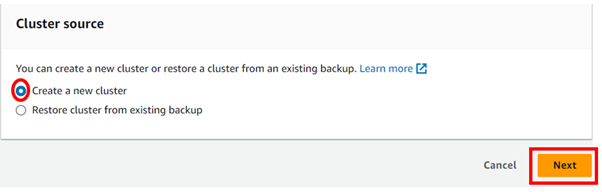
We will create a new cluster, so select the radio button on Create a new cluster then click next.
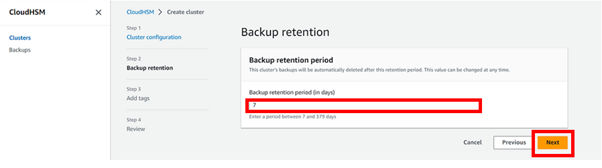
Enter the backup retention period then click next.
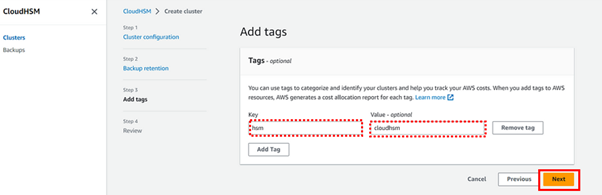
We will tag our HSM.
Review page.
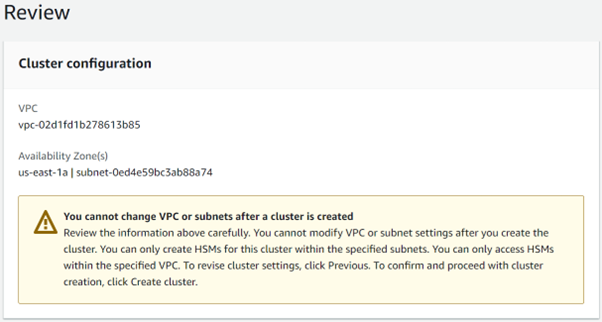
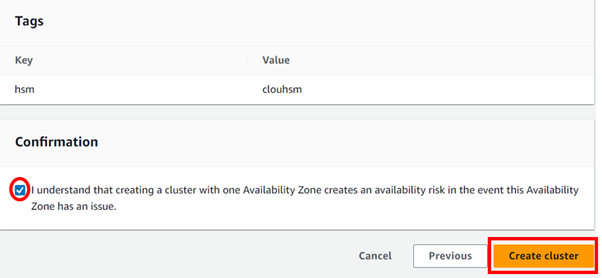
For confirmation, make sure to tick the check box, then hit on the Create cluster.
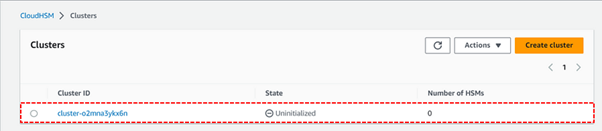
Wait until it gets created complete. And move the status to an uninitialized state.

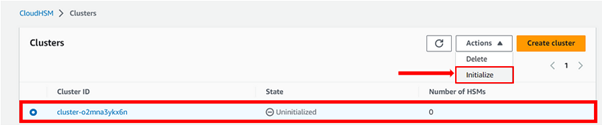
Select the cluster from the actions drop-down button then select initialize.
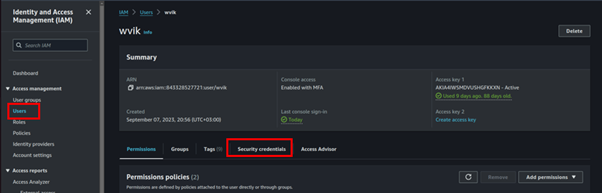
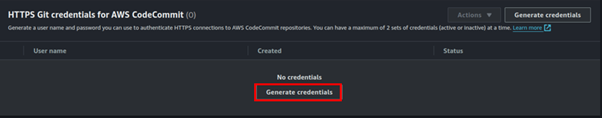
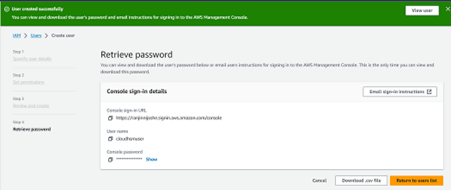
We will now create an IAM user, cloudhsmuser with full access.
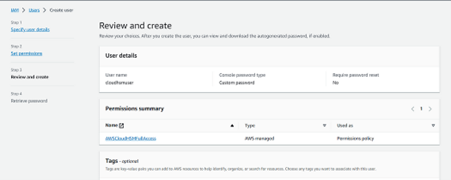
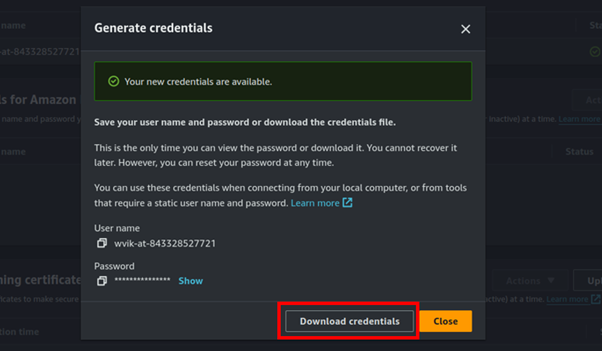
Take note of the password and download the .csv file
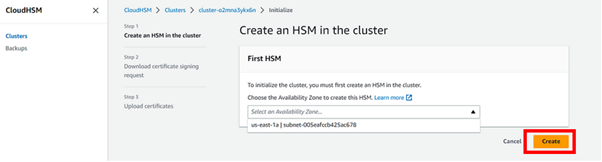
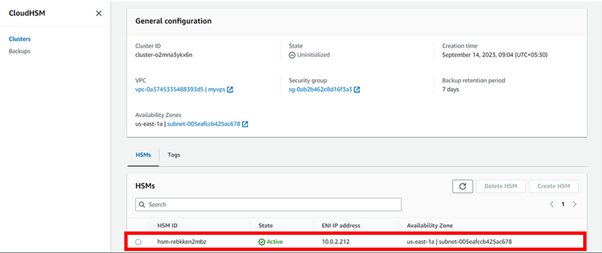
Create HSM in the cluster, select the Availability Zone, and hit on Create.
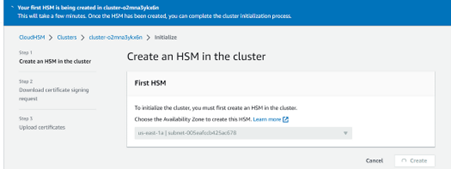
Wait until the process gets completed.
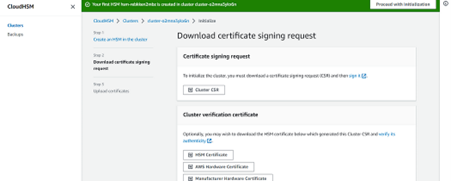
Download all 4 certificates then hit next.
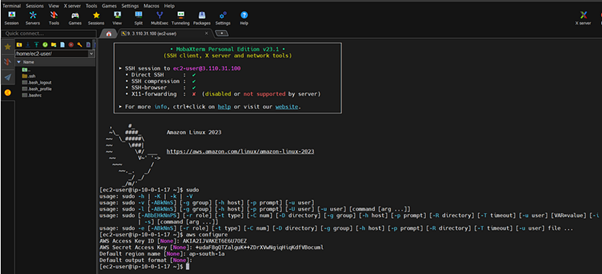
Configure the HSM user on the EC2 machine using Mobastream.
Make sure Cluster is Active. As per the below screen, the Cluster is in an active state.
That’s it. Thumps up.
Conclusion
AWS Hardware Security Module or Cloud HSM provides a powerful solution for secure key management in the cloud. By leveraging hardware-based security, it offers enhanced protection for cryptographic keys, helping organizations meet stringent compliance requirements and protect sensitive data.
This brings us to the end of this blog. Thanks for reading, and stay tuned for more. Make sure you clean resources.
If you have any questions concerning this article or have an AWS project that requires our assistance, please reach out to us by leaving a comment below or email us at sales@accendnetworks.com.
Thank you!