Unveiling the Power of AWS Systems Manager: Simplifying Management and Automation.

Managing and maintaining a fleet of virtual machines and services in the error of cloud computing can be a daunting task. This is where AWS systems manager comes in as a powerful suit of tools designed to simplifying operational tasks, automate workflows and enhance security a cross your AWS infrastructure. In this blog article, we will delve into the capabilities and benefits of AWS Systems Manager.
What is AWS Systems Manager
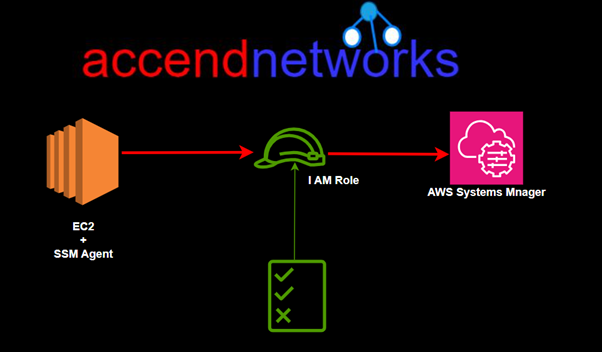
According to AWS documentation, AWS Systems Manager is the operations hub for your AWS applications and resources and a secure end-to-end management solution for hybrid and multicloud environments that enables secure operations at scale. AWS Systems Manager (SSM) is an agent-based service for managing servers on any infrastructure: AWS, on-premise and other clouds.
SSM Agent
The AWS Systems Manager Agent (SSM Agent) is Amazon software that operates on Amazon EC2 instances, edge devices, and on-premises servers and virtual computers (VMs). Systems Manager may update, manage, and configure these resources using the SSM Agent. The agent receives requests from the AWS Cloud’s Systems Manager service and executes them as stated in the request. The SSM Agent then uses the Amazon Message Delivery Service to deliver status and execution information back to the Systems Manager service.
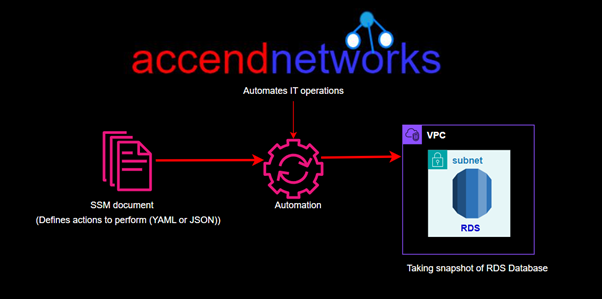
AWS Systems Manager Features Automation
With SSM automation we have something called a document which defines an action to perform and it’s written in YAML or JSON. For instance, we can have a document that creates a snapshot of an RDS database. The documents are fed into the SSM automation which will then automate the IT operations and management tasks across the AWS resources.
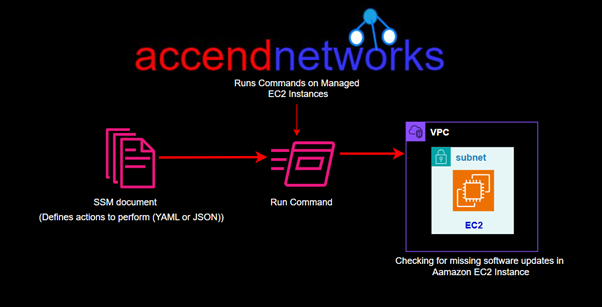
Run Commands
The run command is also very similar, it also has documents. They include things such us commands, automation and packages. For example, we have run command that lists missing Microsoft windows updates, find out what they are and be able to patch them.
Inventory
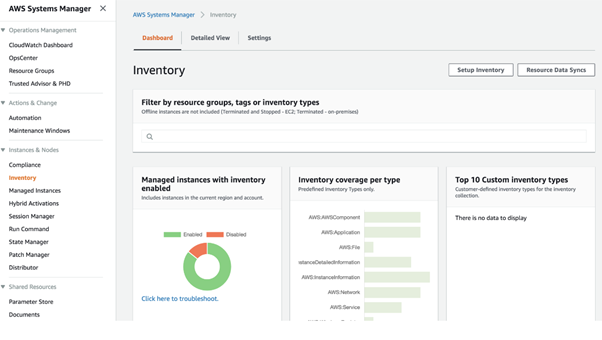
This quit gives you an inventory of resources that you are managing. Once the information is collected, we can gather all that data, visualize it then drill down into the various components of the inventory.
Patch Manager
Helps you select and deploy operating systems and software patches across large groups of Amazon EC2 and on-premises instances.
We have something called patch baselines where we can set rules to auto approve select categories of patches to be installed, specify a group of patches that override these rules and are automatically approved or rejected.
We can also specify maintenance windows for patches so that they are only specified during predefined times.
Patch manager helps to ensure that your software systems are up to date and meets your compliance policies you might have in your organisation.
SSM helps you scan your managed instances for patch compliance as well as configuration inconsistencies.
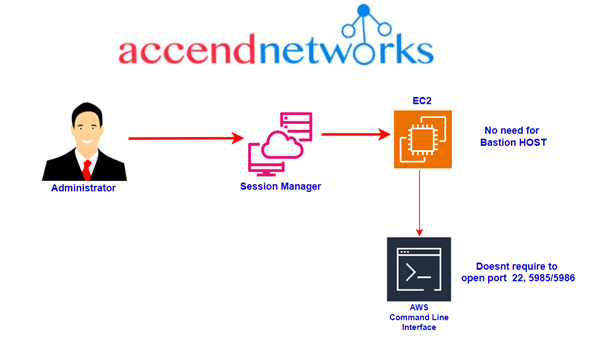
Session Manager
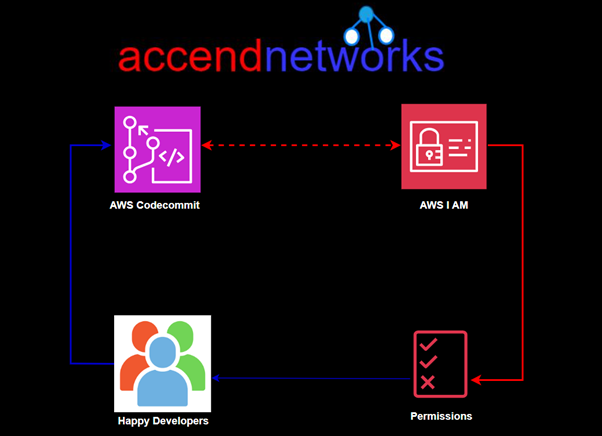
Allows you to connect to the command lines on your instances enabling secure management of instances at scale without logging into your servers. It replaces the needs for Bastion hosts, SSH or Remote PowerShell.
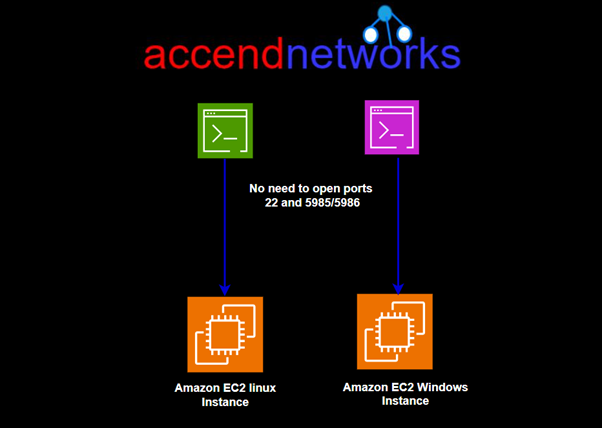
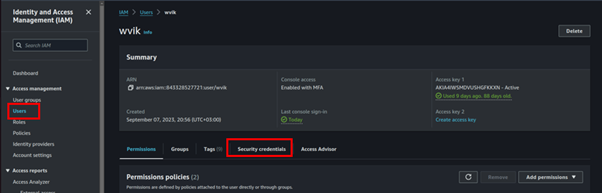
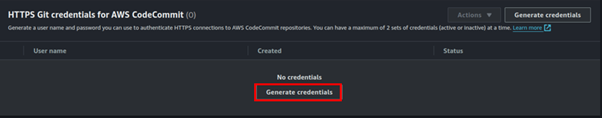
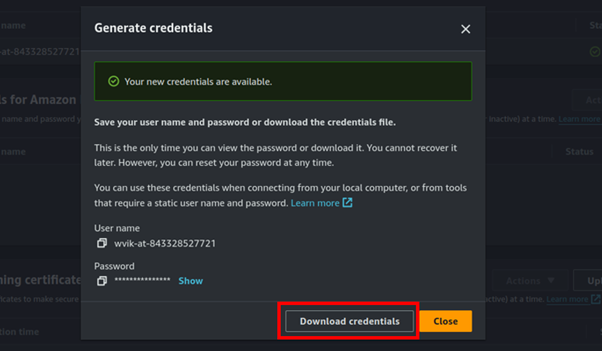
This means you don’t open ports you typically need for these protocols. It also integrates with I AM for granular permissions and all the actions that are taken can be seen in AWS cloud Trail. You can store your session logs in AWS S3 and have outputs go to Amazon CloudWatch logs as well.
To enable this to work you need I AM permissions for EC2 instance to access SSM, S3 and CloudWatch logs.
Parameter Store
This is a service that allows you to store configuration data and secretes. You can store data such us passwords, database strings and licence codes. Data can be stored in plain text, or cyphertext.
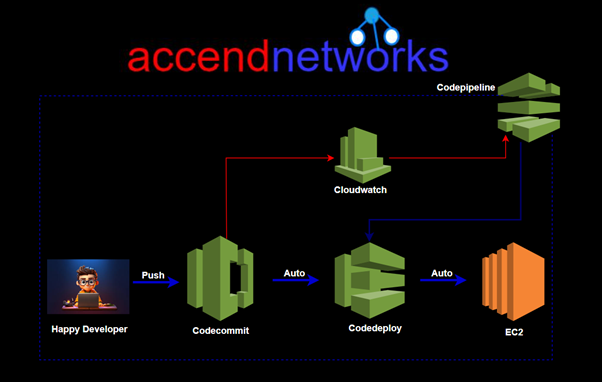
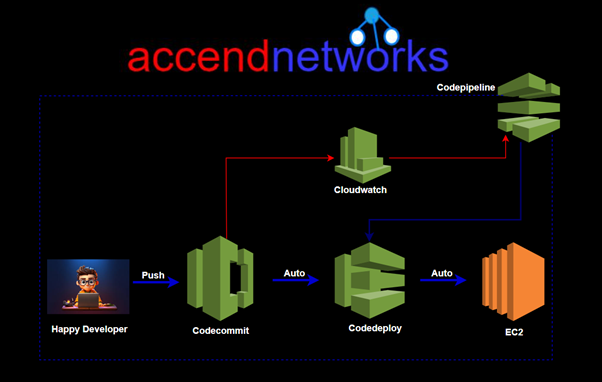
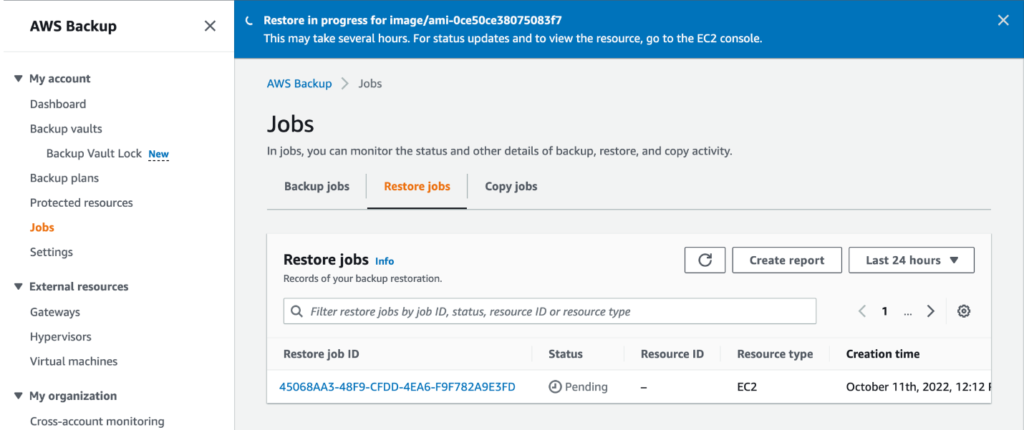
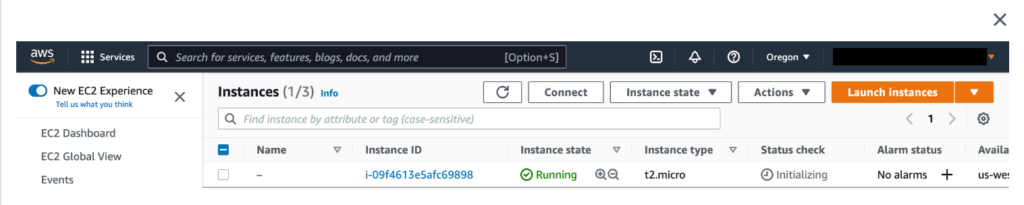
How does Systems Manager work?
Let’s understand with a general example of a systems Manager process flow.
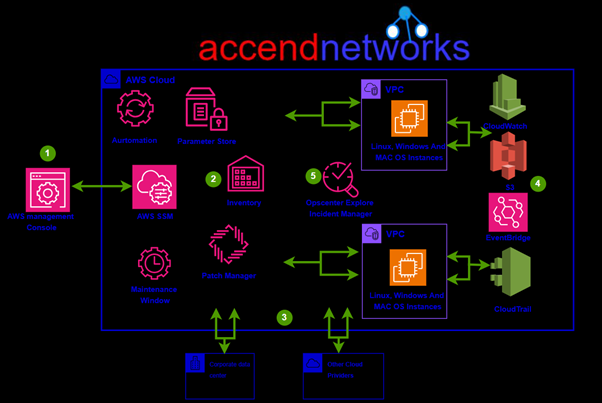
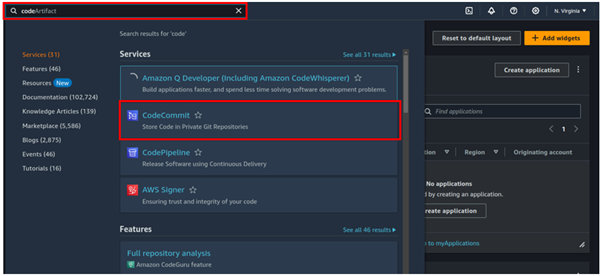
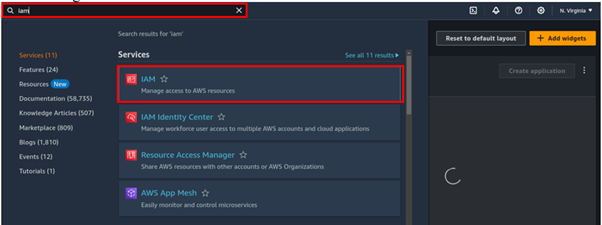
- Access Systems Manager– The AWS Console provides access to the Systems Manager. You can use the AWS Command Line Interface, AWS Tools for Windows PowerShell, or the AWS SDK to manage resources programmatically. You may use Systems Manager to configure, schedule, automate, and execute operations on your AWS resources and managed nodes.
- Choose a systems Manager capability – More than two dozen functions are included in Systems Manager to assist you in performing activities on your resources. Only a handful of the features that administrators employ to configure and manage their resources are shown in the illustration.
- Verification and processing – Systems Manager verifies configurations, including permissions, and makes requests to the AWS Systems Manager agent (SSM Agent) running on your hybrid environment’s instances, edge devices, or servers and VMs. The configuration changes given by SSM Agent are implemented.
- Reporting– SSM Agent notifies the user, Systems Manager in the AWS Cloud, Systems Manager operations management capabilities, and various AWS services, if configured, about the status of the configuration changes and actions.
- Systems Manager operations management capabilities– In reaction to events or issues with your resources, Systems Manager operations management features such as Explorer OpsCenter and Incident Manager aggregate operations data or create artifacts such as operational work items (Ops Items) and incidents if enabled. These features might assist you in investigating and troubleshooting issues.
This brings us to the end of this blog, thanks for reading and stay tuned for more.
If you have any questions concerning this article or have an AWS project that requires our assistance, please reach out to us by leaving a comment below or email us at sales@accendnetworks.com.
Thank you!